Can You Afford a Data Breach?
Could your business recover from that?
Perimeter Security Is No Longer Enough
Every query, prompt, and pipeline decrypts sensitive material into working memory.
RAG pipelines and AI agents pull indiscriminately from connected data sources.
No system controls what AI actually sees — models have root-level visibility into corporate data.
Solution
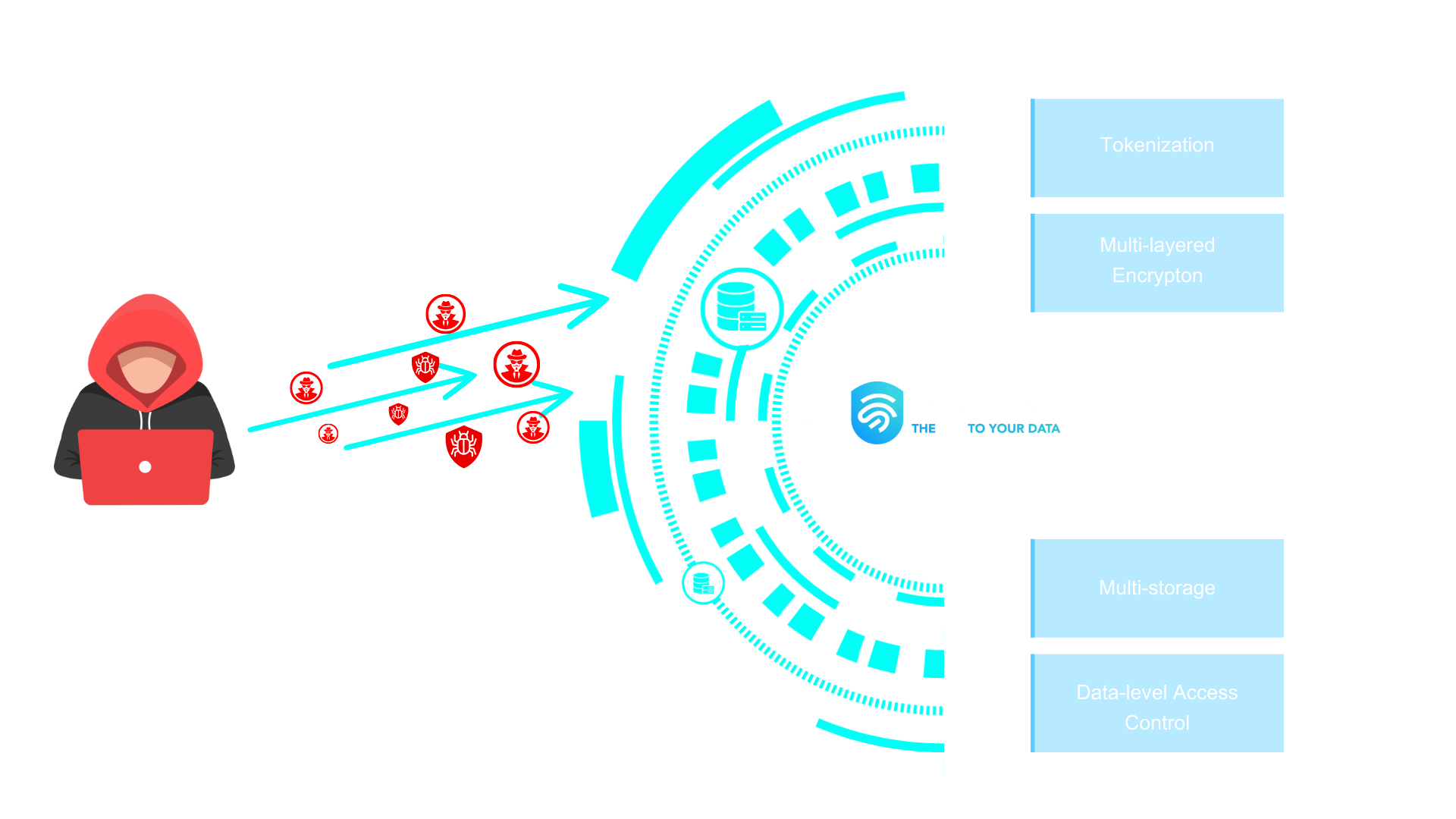
A Data-Level Zero Trust Engine for AI, Humans, and Devices
Privicore controls access to data in real time. Designed for developers.
Post-quantum ready. Built to evolve without architectural change.
End-to-end Data Security in One Platform
Data Privacy Manager (DPM)

Multi Cloud
Databases
Files
Applications
Documents
Back-ups
Ransomware Defense
Data is tokenized and stored in multiple locations, making it nearly impossible for attackers to breach all at once.
Data Loss Prevention
Storing data across different sources significantly reduces the risk of loss.
Unreadable to Intruders
Multiple encryption layers and separate key storage keep data unreadable, even if breached.
Controlled Data Access
Strict access control using trusted devices, biometrics, and location ensures that only authorized users can access data.
Connect
Gather your API details and get ready to start.
Register
Create your application profile in minutes.
Authenticate
Secure your connection with an authorization token.
Tokenize
Protect your data by converting it into secure tokens.
Access & Manage
Retrieve data securely and monitor everything with ease.
Technology Behind PriviCore
Key Management
Without keys, data can’t be decrypted. We store them in multiple locations for added security.
Fast Encryption technology
In combination with tokenization we use a fast and secure elliptic curve encryption method to encrypt data.
Tokenization
Sensitive data like credit card numbers are replaced with tokens, useless to hackers.
Policy & Voting
Device security
Use of an immutable ledger ensures device security and trust.
Storage Decentralization
We separate data storage from encryption keys, reducing the risk of breaches and ransomware.
AI & Machine learning
Policy based learning algorithms and risk profiling.
Secret management & Synchronization
Manage all client’s secret and synchronize data across storage devices.
High transaction volume using Fast Message Queue
Fast acceleration for low latency and fast transactions.
